Which Of The Following Is True Of Transmitting Or Transporting Sensitive Compartmented Information: Essential Guidelines
Transmitting or transporting sensitive compartmented information (SCI) requires strict protocols. Certain rules must be followed to ensure security.
Sensitive Compartmented Information is highly classified. Mishandling it can have severe consequences. Knowing the correct procedures is crucial. Without proper handling, there can be breaches. In this blog, we’ll explore the essential rules for transmitting or transporting SCI. Understanding these rules helps protect valuable information.
Compliance is not just a guideline; it’s a necessity. Let’s dive into the details to ensure we handle SCI properly.
Introduction To Sensitive Compartmented Information
Sensitive Compartmented Information (SCI) is critical to national security. It must be handled with the utmost care. SCI includes highly classified data. Only authorized individuals can access it. Mishandling this information can have severe consequences.
Definition And Importance
SCI is a subset of classified information. It requires special handling and protection.
Definition: SCI is information that needs extra protection within controlled channels. It is not just any classified data. It is the most sensitive.
Importance: SCI protects national security. It covers everything from military secrets to intelligence operations. Proper handling ensures the safety of these operations.
Risks Of Mishandling
Mishandling SCI can lead to severe risks. Unauthorized access can result in:
- National security breaches
- Compromised intelligence
- Endangered lives
Therefore, proper handling and transportation of SCI are crucial.
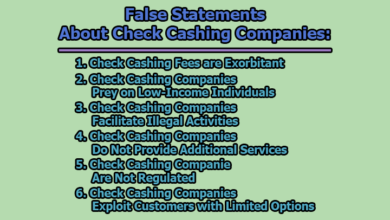
Credit: www.chegg.com
Key Principles For Handling Sensitive Information
Handling sensitive information requires a high level of responsibility and care. This information can include classified data, personal details, or proprietary business secrets. The key principles for handling sensitive information ensure it remains secure and accessible only to those who are authorized.
Need-to-know Basis
One of the primary principles is the need-to-know basis. This means that sensitive information should only be shared with individuals who have a specific need for it to perform their duties. This approach minimizes the risk of unauthorized access and helps maintain the integrity of the information.
- Share information only with those directly involved
- Limit the amount of information shared
- Regularly review who has access
Proper Authorization
Ensuring proper authorization is another critical principle. Individuals must have the correct clearance levels to access sensitive compartmented information. This involves a formal process to verify that a person is trustworthy and has a legitimate reason to access the data.
- Verify the clearance level of each individual
- Use secure methods for verifying identity
- Keep detailed records of who has access
By following these principles, organizations can protect sensitive information from unauthorized access. This helps maintain confidentiality and security.
Methods Of Secure Transmission
Transmitting or transporting Sensitive Compartmented Information (SCI) requires strict methods to ensure security. Various secure transmission methods help in protecting this sensitive data. Here are some of the key methods for secure transmission.
Encrypted Communication Channels
Using encrypted communication channels is crucial for safeguarding SCI. Encryption converts data into a coded format, readable only by authorized parties. It ensures that unauthorized individuals cannot access the information.
- SSL/TLS: Secure Sockets Layer and Transport Layer Security encrypt data during transmission.
- VPN: Virtual Private Networks create secure connections over public networks.
- End-to-End Encryption: This method ensures only the communicating users can read the messages.
Secure File Transfers
Transferring files securely involves using reliable protocols and tools. These methods prevent unauthorized access and data breaches.
| Method | Description |
|---|---|
| SFTP | Secure File Transfer Protocol uses SSH to transfer files securely. |
| FTPS | File Transfer Protocol Secure uses SSL/TLS for encryption. |
| PGP | Pretty Good Privacy encrypts files before transfer. |
To further secure file transfers, use strong passwords and two-factor authentication. Always verify the recipient’s identity before sending sensitive files.
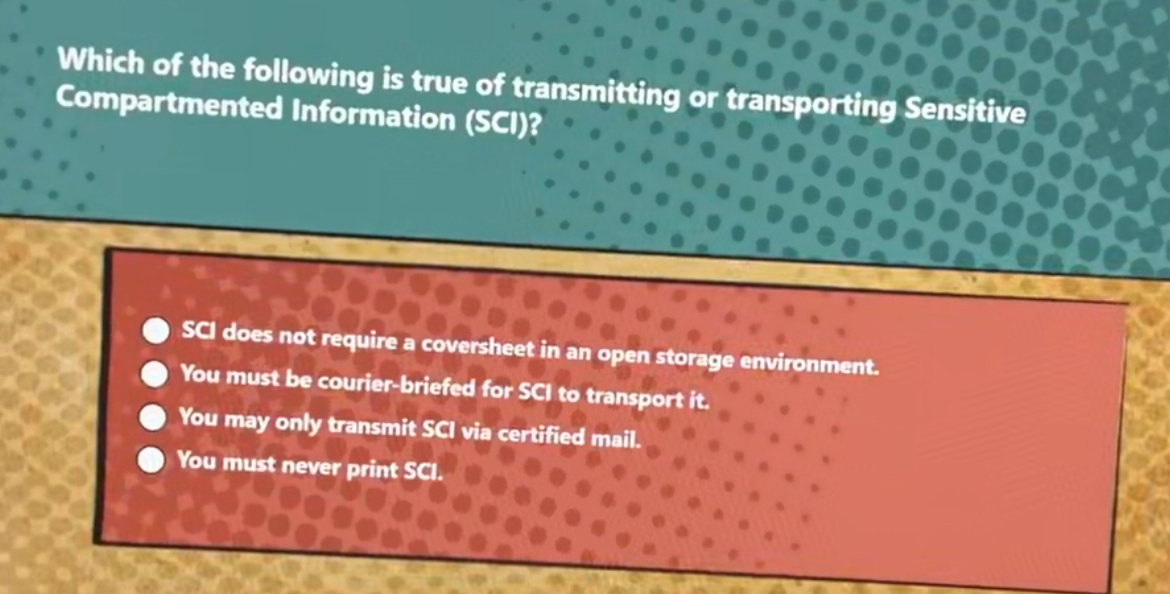
Credit: www.gauthmath.com
Physical Transportation Guidelines
Transporting Sensitive Compartmented Information (SCI) involves strict guidelines. These guidelines ensure the security of the information during physical transportation. Understanding these Physical Transportation Guidelines is crucial. Below, we’ll explore the key aspects of secure packaging and trusted couriers.
Secure Packaging
Packaging SCI properly is vital. Use two layers of secure packaging. The inner layer should be a strong, tamper-evident material. The outer layer must conceal any classified markings.
Here is a simple table to illustrate the packaging requirements:
| Layer | Material | Purpose |
|---|---|---|
| Inner | Tamper-evident material | Protect and secure the contents |
| Outer | Non-descript material | Conceal classified markings |
Trusted Couriers
Always use trusted couriers for transporting SCI. These couriers should have proper clearance and training. They should understand the importance of the information they are carrying.
- Couriers must have the required security clearance.
- They should be trained in handling SCI.
- They must follow strict protocols during transportation.
Using trusted couriers reduces the risk of information leaks. It ensures that SCI reaches its destination safely.
Digital Security Measures
Transmitting or transporting Sensitive Compartmented Information (SCI) requires robust digital security measures. These measures ensure data stays secure and out of unauthorized hands. Here, we will explore two essential digital security measures.
Use Of Vpns
Virtual Private Networks (VPNs) are critical for protecting SCI. They create a secure connection over the internet. VPNs encrypt data, making it unreadable to hackers. Using VPNs adds a strong layer of security. This is vital for anyone handling sensitive information.
Two-factor Authentication
Two-Factor Authentication (2FA) is another essential security measure. It requires two types of identification before access. Usually, this means entering a password and a code sent to your phone. 2FA ensures that even if a password is stolen, the data remains protected. This method is simple yet highly effective for securing SCI.
Role Of Training And Awareness
Training and awareness are vital in handling sensitive compartmented information (SCI). Effective training programs ensure employees understand the importance of security measures. Awareness initiatives help prevent unintentional breaches.
Regular Security Training
Regular security training is crucial. Employees must stay updated on the latest protocols. This includes understanding how to handle SCI securely. Training sessions should cover:
- Proper document storage
- Secure communication methods
- Access control procedures
Maintaining a regular training schedule helps reinforce security practices. Employees must know the risks and how to mitigate them.
Recognizing Phishing Attacks
Recognizing phishing attacks is essential. Phishing is a common method used to access SCI. Employees should be trained to identify phishing attempts. Key indicators of phishing include:
- Suspicious email addresses
- Urgent or threatening language
- Unexpected attachments or links
Training sessions should include real-world examples of phishing. This helps employees understand what to look for. Regular updates on new phishing tactics are also important.
Incident Response And Reporting
Handling Sensitive Compartmented Information (SCI) requires strict protocols. If an incident occurs, taking the right steps is crucial. Proper incident response and reporting ensure that sensitive data remains secure. This section outlines immediate action steps and reporting protocols.
Immediate Action Steps
First, identify the breach or incident quickly. Assess the situation to understand the severity. Then, isolate the affected systems to prevent further damage. Do not attempt to fix the issue yourself. Contact the designated security personnel immediately. Follow their instructions carefully. Document everything you observe during the incident.
Reporting Protocols
Report the incident to the appropriate authority without delay. Use the established communication channels for reporting. Provide all necessary details, including time and nature of the incident. Include any actions taken before the report. Ensure the information is accurate and complete. Maintain confidentiality throughout the reporting process. Follow up as instructed by the security personnel.

Credit: www.docsity.com
Best Practices And Common Mistakes
Transmitting or transporting Sensitive Compartmented Information (SCI) requires strict adherence to best practices. Mishandling SCI can have severe consequences. Avoiding common mistakes ensures the information remains secure. Here are some best practices and common mistakes to consider.
Regular Audits
Conduct regular audits to ensure compliance with security protocols. Audits help identify potential vulnerabilities. They also ensure all personnel follow the established guidelines. Use audits to review security measures and update them as needed. Regular checks help maintain a high security standard.
Avoiding Complacency
Never become complacent with SCI handling. Always stay vigilant and follow protocols. Complacency can lead to security breaches. Ensure continuous training for all personnel involved with SCI. Regular reminders and updates keep security at the forefront. Stay alert to new threats and adjust practices accordingly.
Frequently Asked Questions
What Is Sensitive Compartmented Information (sci)?
Sensitive Compartmented Information (SCI) is classified information concerning or derived from intelligence sources, methods, or analytical processes. It is highly restricted.
How To Properly Handle Sci?
Handle SCI in a secure environment, using approved communication channels. Always follow established protocols to prevent unauthorized access.
Can Sci Be Transmitted Electronically?
Yes, SCI can be transmitted electronically but only through secure, encrypted communication systems approved for handling such sensitive information.
What Are The Risks Of Mishandling Sci?
Mishandling SCI can result in severe national security risks, unauthorized disclosures, and potential legal consequences for individuals involved.
Conclusion
Transmitting sensitive compartmented information demands strict protocols. Always use secure channels for communication. Unauthorized access can lead to serious consequences. Encrypt data during transmission. Verify recipient identity. Constant vigilance is key. Adhere to guidelines and ensure information safety. Secure handling protects national security.
Follow best practices to avoid breaches. Stay informed and compliant.